Manufacturing Automation & Technology Solutions
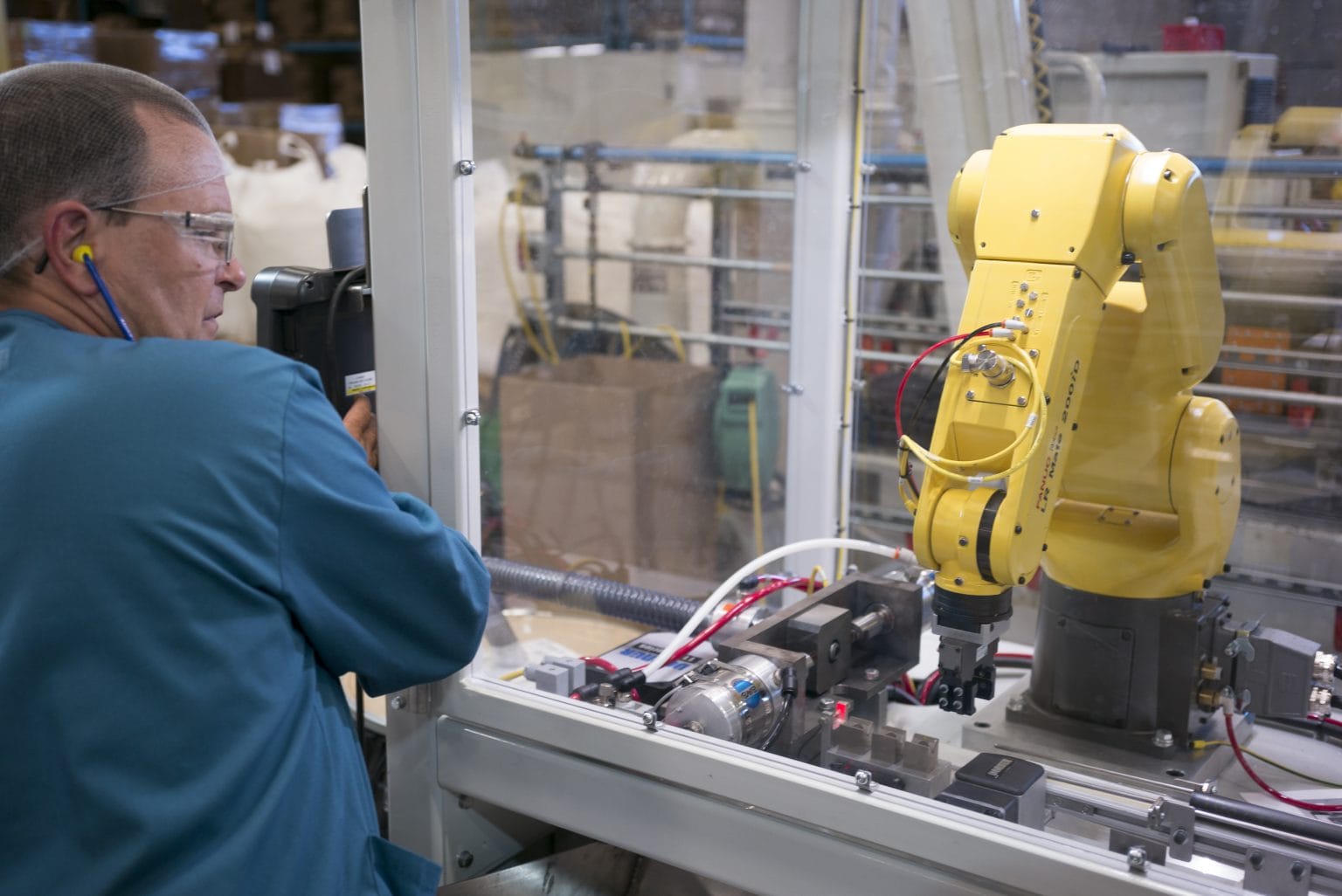
Automation Services & Assessments
Implement automation that provides the maximum business impact. We help manufacturers:
- Become more competitive
- Increase productivity
- Increase performance
- Grow profits and value
- Reduce labor impacts
The WMEP Automation Assessment provides a path for manufacturers to evaluate potential automation projects. Our consultants will visit your facility to help you:
- Understand and manage potential automation project risk
- Align projects with business strategy
- Calculate ROI for projects
Your existing applications and processes will be evaluated for potential future state automation. The assessment will include potential ROI rankings based on your manufacturing environment, personalized to your business case.
A Wisconsin Automation Implementation Grant is available for qualifying companies. Participation is limited. Learn more at this link.
View Infosheet | View Case Studies
Click here to review Colin Wilson and George Bureau’s September 2022 – Wisconsin Automation, Technology & Systems Pulse Survey Findings.
Deliverables
- Risk rankings for potential automation projects based on real world observation
- ROI analysis and feedback
The WMEP Automation Assessment Express service is designed to evaluate up to three key processes for automation technology fit, risk, and ROI. The Assessment Express targets bottleneck, labor-intensive, or client-requested processes for evaluation.
AutomationTech™ demystifies manufacturing automation options by educating, assessing, and developing an action plan that is right for your company. Manufacturers across the automation spectrum attend — both the manufacturer just starting down the automation path and the automated manufacturer who is resource limited to determine project priority. Manufacturers will leave with a unique Automation Action Plan as a roadmap for investment in automation that supports their business strategy.
The program is a series of four half day workshops and onsite visits within a 3-month period.
Deliverables
- Onsite automation assessment: one-on-one
- Road map to developing an Automation Action Plan
- Project risk rankings
- Support resource identification
- Business strategy evaluation
- ROI calculator package
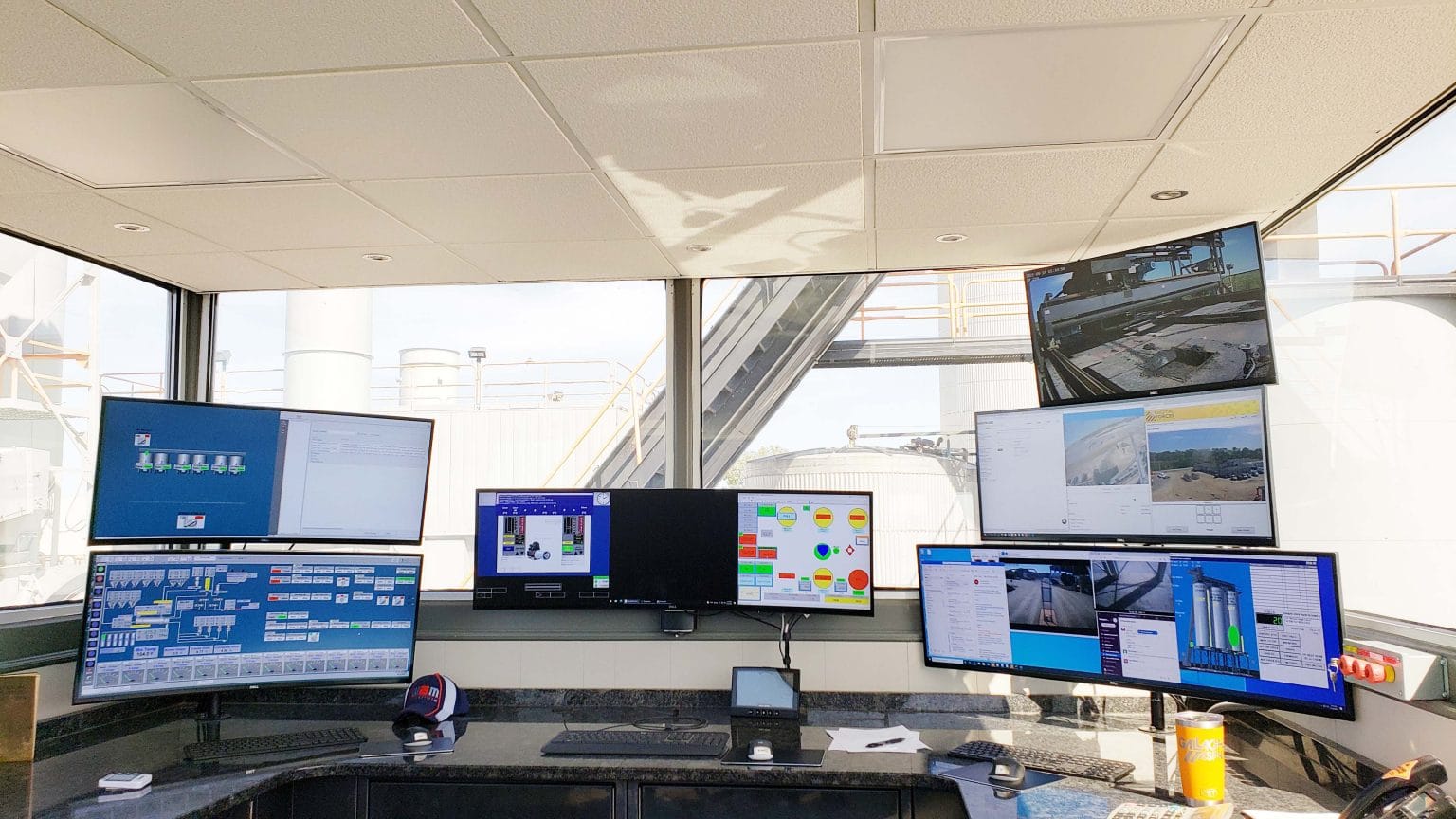
The IT-OT Integration Service provides a process for connecting manufacturing equipment to acquire information and analyze it to make data driven decisions through:
- Adding intelligence to machines to collect data from them.
- Identifying methods to connect various pieces of equipment like CNC machines,
- Industrial robots, PLC or PC controlled equipment.
- Utilizing various storage methods including on premises and cloud-based solutions.
- Incorporating process for visualizing and analyzing data.
- Integrating Cybersecurity best practices to secure business networks and data
Benefits
- Increase output and efficiency by developing a more strategic production plan
- Reduce downtime by planning for Preventative or Predictive Maintenance
- Definitively estimate consumable usage and tool wear
- More accurately troubleshoot quality and process related issues
- Resolve issues in real-time using data driven escalation plans
The WMEP AutomationAdvisor™ service synchronizes with manufacturers by assessing, developing an action plan, and initiating automation projects. Manufacturers who have some experience with automation — whether positive or negative — can benefit from the service.
Program Description:
A WMEP Automation Consultant will evaluate the manufacturing process onsite and perform an Automation Assessment.
An Automation Action Plan is then co-developed with the manufacturer based on their business strategy that aligns with internal initiatives.
After a direction is decided, the WMEP Automation Consultant assists the manufacturer to define the project scope and initiate RFQs. Responses to the RFQs are vetted and the consultant will assist in developing a training plan for project support.
Deliverables
- Onsite automation assessment: one-on-one
- Automation project risk ranking
- Automation ROI rankings
- Automation action plan development
- Recommend third party integrators
- Mutually written RFQ/statement of work
- Evaluate third party proposals
- Provide example automation project PM
- Training plan for equipment support
Cybersecurity
The WMEP’s experienced team has designed a comprehensive four-step cybersecurity program. We will help you gauge your current situation and tailor a plan specifically for your internal capabilities, budget, and time sensitivity.

How our cybersecurity approach works
1
Discovery
The professional assessment of your company’s practices related to the new standard. If necessary, a gap analysis will be completed to document the scope to be remediated.
2
Remediate To Meet New Standard
Supports all necessary fixes to ensure compliance. This may include updates to firewalls, patches, policy development, employee training, physical security, network configuration, etc.
3
Test and Validate
Verifies that all technology and physical security aspects are working properly. A penetration test may be necessary.
4
Monitoring & Reporting
Establishes ongoing monitoring and scanning of the required enterprise network. Creates a working process to log, remediate and report (as required) cyberattacks.
Technology Services & Assessments
WMEP helps manufacturers accelerate their business growth and sustain success into the future. We analyze new and existing technology to develop a framework for secure business operations.
Technology Scouting identifies technologies to expand your product base, helping you bring more value to your customers and serve new markets. It is ideal for manufacturers who want to bring a technology in house or are trying to bring additional product options to customers.
Benefits
- Give you access to research on available technologies
- Uncover low-risk parallel paths of product development
- Help you gain focus to expand beyond your current products
- Minimize investment risk by developing alternative paths, including outsourcing, new equipment, or equipment modification
- Give you the ability to bid on different or expanded scope jobs, allowing you to earn new customers
- Bring new products to your clients
- Help you discover new technologies to service an existing market
Technology-Driven Market Intelligence (TDMI) is the link between your unique technology and new customers who need that technology.
Benefits
- Give you an unbiased review of your technology and market
- Provide expert research utilizing member-only databases
- Offer expertise from interviews with industry leaders and potential customers
- Generate a plan with multiple solutions and outcomes
- Prioritize ideas to eliminate false paths
- Provide a clear direction for progression
- Identify a prospective client list

Get to know Mark Hatzenbeller
Director of Business Development
Mark has 40 years of experience leading efforts to develop integrated solutions that solve key manufacturer challenges.

Get to know Colin Wilson
Senior Consultant – Automation
Colin has worked with small manufacturers just starting down the automation path, to multinational corporations optimizing their value stream.